The scripts in the tools/gate directory do not run ansible with a local conenction; the ansible playbooks attempt to SSH to a VM on localhost and fail. This change adds the local connection flag in order to run directly on the host. Change-Id: I3d7c7b6d21fc4972bd8a084ea49c945af4bfc518 Signed-off-by: Drew Walters <andrew.walters@att.com>
airshipctl
What is airshipctl
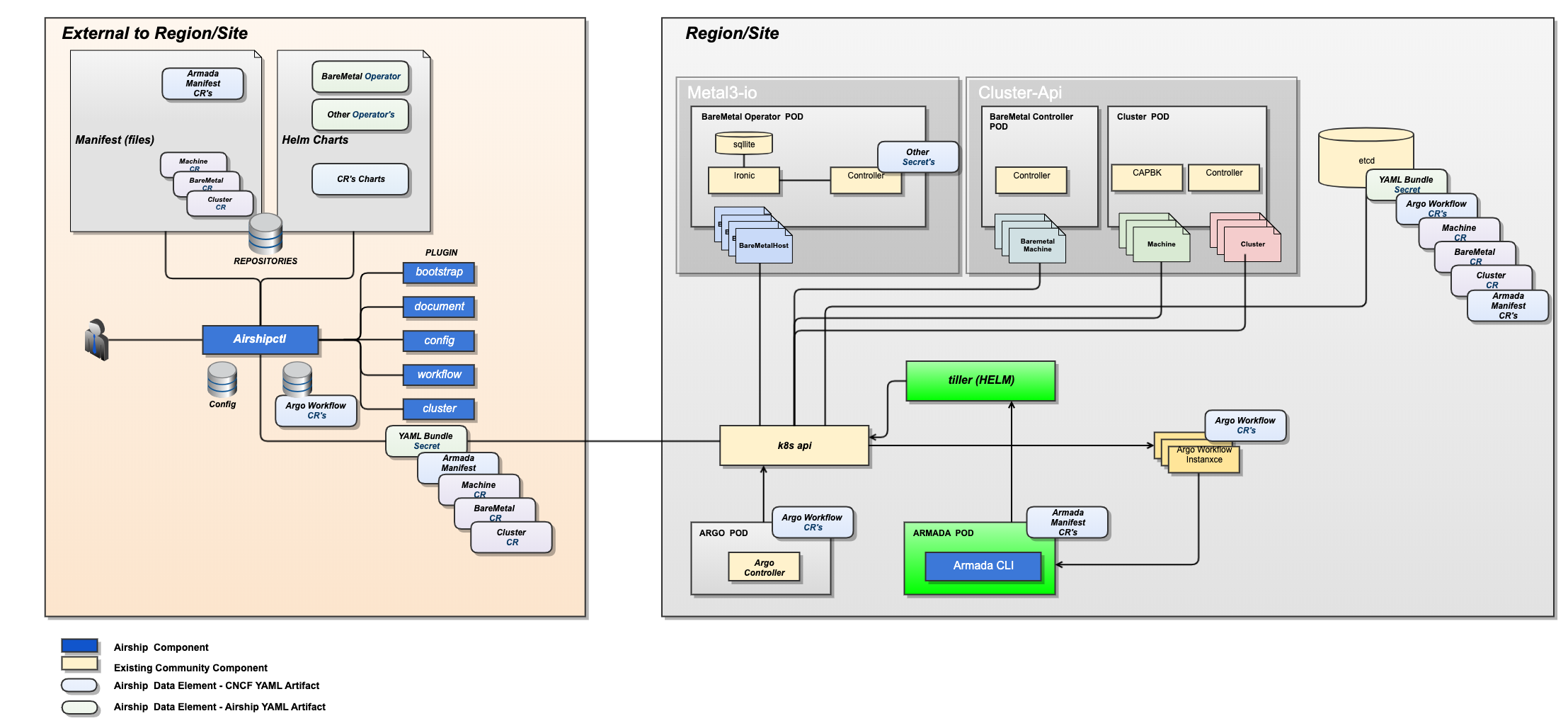
The airshipctl project is a CLI tool and Golang library for declarative
management of infrastructure and software.
The goal for the project is to provide a seamless experience to operators wishing to leverage the best of breed open source options such as the Cluster API, Metal3-io, Kustomize, Kubeadm, and Argo -- into a straight forward and easily approachable tool.
This project is the heart of the effort to produce Airship 2.0, which has three main evolutions from 1.0:
- Expand our use of entrenched upstream projects.
- Embrace Kubernetes Custom Resource Definitions (CRD) – Everything becomes an Object in Kubernetes.
- Make the Airship control plane ephemeral.
To learn more about the Airship 2.0 evolution, please check out the Airship Blog Series.
Contributing
This project is under heavy active development to reach an alpha state.
New developers should read the contributing guide as well as the developer guide in order to get started.
Architecture
The airshipctl tool is designed to work against declarative infrastructure
housed in source control and manage the lifecycle of a site.
Example Usage
In a nutshell, users of airshipctl should be able to do the following:
- Create an
airshipctlAirship Configuration for their site - sort of like a kubeconfig file. - Create a set of declarative documents representing the infrastructure (baremetal, cloud) and software.
- Run
airshipctl document pullto clone the document repositories in your Airship Configuration. - When deploying against baremetal infrastructure, run
airshipctl bootstrap isogento generate a self-contained ISO that can be used to boot the first host in the cluster into an ephemeral Kubernetes node. - When deploying against baremetal infrastructure, run
airshipctl bootstrap remotedirectto remotely provision the first machine in the cluster using the generated ISO, providing an ephemeral Kubernetes instance thatairshipctlcan communicate with for subsequent steps. This ephemeral host provides a foothold in the target environment so we can follow the standard cluster-api bootstrap flow. - Run
airshipctl cluster initinfra --clustertype=ephemeralto bootstrap the new ephemeral cluster with enough of the chosen cluster-api provider components to provision the target cluster. - Run
airshipctl clusterctlto use the ephemeral Kubernetes host to provision at least one node of the target cluster using the cluster-api bootstrap flow. - Run
airshipctl cluster initinfra --clustertype=targetto bootstrap the new target cluster with any remaining infrastructure necessary to begin running more complex workflows such as Argo. - Run
airshipctl workflow submit sitemanageto run the out of the box sitemanage workflow, which will leverage Argo to handle bootstrapping the remaining infrastructure as well as deploying and/or updating software.
As users evolve their sites declaration, whether adding additional
infrastructure, or software declarations, they can re-run airshipctl workflow submit sitemanage to introduce those changes to the site.
Project Resources
- Airship Website - airshipit.org
- Airship UI Project - opendev.org/airship/airshipui
- airshipctl Issue Tracker - https://github.com/airshipit/airshipctl/issues